Apple’s security protocol puncture is almost as grave as giving your credit card straight to a hacker instead of making them steal the information through the magnetic stripe readers.
The bug in Apple’s iOs and OS X platforms basically permits a hacker to get in between the initial verification “handshake” connection between the user and the destination server, enabling the attacker to disguise as a trusted endpoint. This means the connection which is meant to be encrypted between you and your bank, email server, healthcare provider and more is potentially vulnerable to attack.

Secure Sockets Layers, and more recently, Transport Layer Security protocols have protected web users for years by creating a digital secure handshake to identify and encrypt data from the browser to the secure end site. The Apple flaw puts hackers in the middle of that handshake, by allowing the SSL/TSL routines to be bypassed.
Security experts across the web advise updating iPhones and iPads with the available iOS patches now, as well as avoiding the use of Safari for OS X systems without an available Apple fix and use other browsers for the time being.
Usually to achieve encrypted web traffic, a handshake is obtained through a Secure Sockets Layer (abbreviated as SSL) or more recently, Transport Layer Security (TLS) ; both are Internet protocols that provide a secure channel between two machines operating over the Internet or an internal network.
The full austerity of the security glitch has yet to emanate, but the duplicated line of code which is prompting all the disturbance has been in place since September 2012. This means theoretically that if you’ve been using the flawed iOS or OS X systems since then, a hacker on your shared network could have captured all your data that should have been SSL (or TSL) encrypted for the past 18 months.
Now take a seat and think of all the banking, online dating, email writing and Internet purchases you’ve made in the last year and a half.
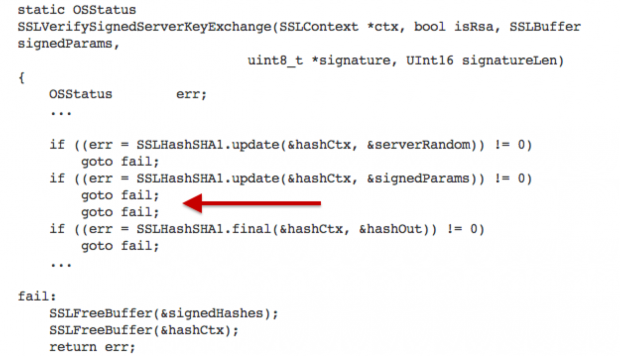
The duplicated line of code that caused the Apple fail is shown here, and now dubbed on Twitter as #gotofail. (Image via Gizmodo)
The SSL/TLS effort beseeches almost zero interaction from us (the end users), however, you may be acquainted with the little lock icon that appears on the browser, indicating a secure connection has been achieved. This is where the Apple flaw steps in; anyone using the same network connection (the person sitting next to you at the coffee shop or at work right now) could fake the secure connection and hijack communication between your browser and a site.
What’s more horrifying, the flaw permits for modification of the “data in flight”; which means in plain English that a hacker could deliver exploits to take control of your system, according to Crowdstrike. Other apps that you may not instantly associate with Internet browsing are influenced as well.
Here are some of the apps which rely on the vulnerable Apple #gotofail SSL library beyond Safari /cc @a_greenberg pic.twitter.com/ombDOOa01A
— ashkan soltani (@ashk4n) February 23, 2014
Apple did release a fix to the flaw harbored in iOS6 and 7 authentication logic, yet the company only states the OS X fix is coming “very soon,” according to Reuters. This indicates Mac desktops and notebooks are still exposed to man-in-the-middle attacks.
Apple’s support page says the company will not “disclose, discuss, or confirm security issues until a full investigation has occurred and any necessary patches or releases are available”. It does, however, describe the fail was addressed by “restoring missing validation steps.”
Apple did not immediately acknowledge TheBlaze for clarification on how swift fixes for Mac desktops and notebooks will be available.
So, are you still on board the iOS ship or will you trade sides for Android?